[post-views]
Congratulations! You made it! You achieved it. Now make sure you secure it.
If you just passed an exam and had an urge to post a picture with your certificate or if you just retired or were just hired by your dream company, you posted a picture of your ID card or your certification, then this article is for you. Hundreds of these pictures are now showing up online on websites that are soliciting fake degrees, certifications, jobs, and more.
While you are proud of your accomplishments make sure you do not post your photos publicly which reveals your name, certificate, and other details. A photo with a face and a certificate in your hands can be used to advertise anything and an acquaintance of mine recently shared a disturbing story.
This individual, whom I call Mr. Good. had recently passed his CISSP exam and like most of us, had posted it on LinkedIn. Mr. Good is a very private person normally but LinkedIn is a social community that he spends most of his time socializing. Thanks to tens of different controls on privacy on LinkedIn, it has gotten even more confusing when you post an update. So out of mere excitement and innocence, he posted his picture. He was proud. A few days later, he discovered, by accident, a photo circulating on Facebook with several others soliciting the sale of illegal certificates such as CISSP and other exams.
That was it for Mr. Good, he immediately removed his picture from his post. But wait, his stolen photo from LinkedIn is being used by someone claiming to be him. Mr. Bad did not even bother to blur out Mr. Good’s name on the certification photo. This would take several attempts, which included contacting Facebook to remove this post. While Facebook is looking into his query, which by the way is probably 1 in a million. It will continue to be online until it is removed.
Here are some examples that I found online.
Real Example 1:
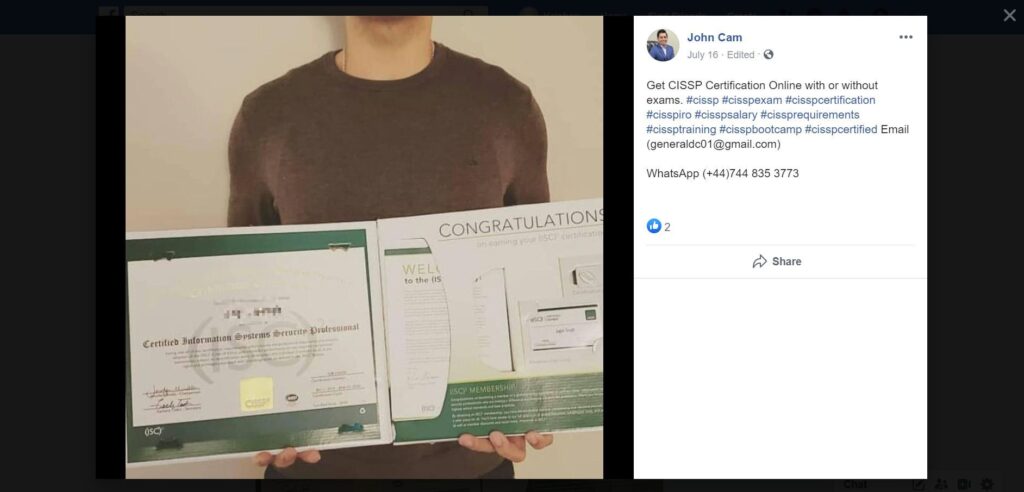
John Cam (Fake Name) claims to sell CISSP Certificates on Facebook with the image on the side. He was a little generous and clipped the picture to remove the face. Image1 is taken from a publicly posted image on LinkedIn profile post, Image 2.
I have pixelated the face to protect the individual.

Real Example 2:
Here is the same individual who is selling illegal certifications, this time it is IELTS Certifications without writing the exam. Not sure how it works or if it is a money-making scheme by fraud.
I have already reported this individual on Facebook but upon doing a simple web search, I found this individual/group has posted at several popular web services such as TripAdvisor, Pinterest, Medium.

What can you do?
If you come across such advertisements or postings, simply report as Spam or use the methods provided. For example, TripAdvisor provides an option on a photo to report. Pinterest provides a feature on their pins and users to be reported.
Do not take photos of your employer ID cards, Certificates, and Degrees and post them publicly. I understand we all have a tendency to post on social media such as LinkedIn, Facebook, Instagram but think about the profound negative effects on your identity if these posts and images were exploited.
Over and Out! Stay safe, think before you click (anywhere).

If you would like to subscribe to this blog. Simply follow me on LinkedIn or Twitter and you will see any new alerts and posts directly on these two platforms.
